After seeing the video titled Two Guitarists, One Melody, my coworker Steve and I decided to replicate this experiment.
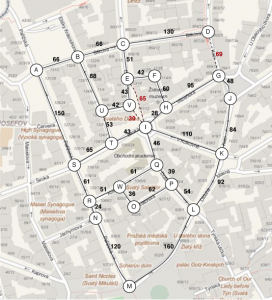
The basic premise is that one person would send two bars of melody to the other, the other person would continue with two bars of their own, and keep going back and forth until we had 16 bars of pure melody.
As you can see from the image above, our melody was a little bit more complex than what you see in the original video that was the inspiration. We tried to throw each other some deliberate curve balls (hello flats!), timings and 16th notes.
Once the melody was complete, each of us would independently try to incorporate it into our own song. Neither of us knew the direction we were taking this song until it was fully completed and produced.
Naturally, what Steve and I came up with sounded very different and distinct with an underlying similarity. Steve went with a dark piano theme while I opted for a Trans-Siberian Orchestra inspired heavy metal Christmas jingle.
Without further ado, here are our respective songs.
Steve:
Me: